Update: This popular deal is still available.
Firebat Online Store via AliExpress has
FIREBAT AM02 Mini PC on sale for $251.27 - $35 when you apply promo code
JJY35 or
USCD35 at checkout =
$216.27.
Shipping is free.
Thanks to community member
shivster1796 for sharing this deal.
- Note: Price may fluctuate slightly with currency exchange rates. You must be signed into your AliExpress account and have your address added to add items to your cart and place an order. You may have to manually type in the promo code to apply it at checkout. This item ships from a USA warehouse. For expedited customer service, please email [email protected].
Specs:
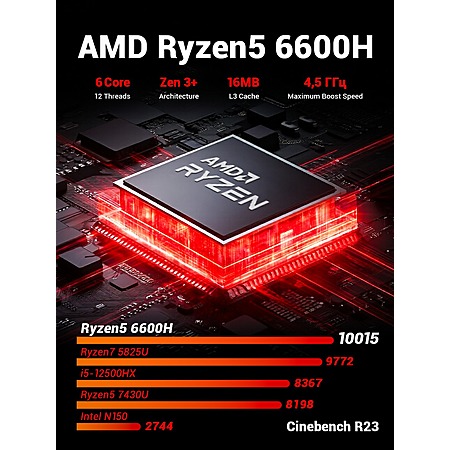
- AMD Ryzen 5 6600H 6-Core / 12 Thread Processor
- 16GB 6400 MHz LPDDR5 Memory / RAM (soldered)
- 512GB M.2 2280 PCIe 4.0 NVMe Solid State Drive
- AMD Radeon 660M integrated graphics
- WiFi 6 + Bluetooth 5.2
- Windows 11
- Supports up to 3 displays (HDMI + DisplayPort + USB-C)
- Ports:
- 3x USB 3.2 Type-A
- 1x USB 2.0 Type-A
- 1x 3.5mm Audio
- 2x 1Gbps LAN
- 1x USB Type-C (w/ DisplayPort support)
- 1x HDMI 2.0
- 1x DisplayPort 2.0



Leave a Comment
Top Comments
Perfect for homme, office, emulation and light PC gaming.
Having x2 m.2 ports means that you could sacrifice one to add an m.2 adapter and use an eGPU for a massively better gaming performance.
Soldered RAM is the only bummer, BUT 16gb is plenty and I think that is the reason that these are so cheap, which is a win.
104 Comments
Sign up for a Slickdeals account to remove this ad.
- Make sure you twist it around in a few directions and open it before turning it on if you hear something -- the screw for the second M.2 drive bay was rolling around inside and could have easily shorted out or damaged surface mount components/solder pads/via's.
- I swapped the drive for an empty spare and installed an old version of Win10 Home on it that I had on USB stick, and it seemed to auto activate.
- Ram is installed in quad-channel layout (confirmed by CPU-Z); 4x separate Micron branded 4GB.
- There is a spot to mount a 2.5 SATA in the bottom cover with side screw holes. However zero way to connect. (After receiving the unit, I can confirm the M.2 slots ONLY support the NVMe protocol and do NOT support any SATA signaling, so no flavors of converters featuring M.2 NVMe to SATA with boost circuit to a sata power cable will work at all with this unit. NVMe only. And I also was only detecting 2500Mbps throughput with them as they are just PCIe 3.0
- Bottom case cover easy to remove, no removing rubber feet, has holes in center of them already.
Perf test results:- Geekbench: CPU Single: 1969, Multi: 7883. GPU OpenCL: 14674 Vulkan: 18468. About 5-8% higher than average 6600H GB scores on CPU
- Passmark: 4606 overall (20314 total CPU, 3374 single threaded CPU sub tile). About 7-11% higher than average 6600H PM scores.
- CPU-Z: 629 single thread, 4729 multi-thread
My AM02/6600H, compared to the F1 7640HS "Average" scores on GB and PM, the F1 CPU is faster by:- Make sure you twist it around in a few directions and open it before turning it on if you hear something -- the screw for the second M.2 drive bay was rolling around inside and could have easily shorted out or damaged surface mount components/solder pads/via's.
- I swapped the drive for an empty spare and installed an old version of Win10 Home on it that I had on USB stick, and it seemed to auto activate.
- Ram is installed in quad layout; 4x separate Micron branded 4GB.
- There is a spot to mount a 2.5 SATA in the bottom cover with side screw holes. However zero way to connect, unless you get a low profile M.2 NVMe to SATA with boost circuit to a sata power cable. Only $2-$3 on AliExpress, have one on the way.
- Bottom case cover easy to remove, no removing rubber feet, has holes in center of them already.
Perf test results:- Geekbench: CPU Single: 1969, Multi: 7883. GPU OpenCL: 14674 Vulkan: 18468. About 5-8% higher than average 6600H GB scores on CPU
- Passmark: 4606 overall (20314 total CPU, 3374 single threaded CPU sub tile). About 7-11% higher than average 6600H PM scores.
- CPU-Z: 629 single thread, 4729 multi-thread
My AM02/6600H, compared to the F1 7640HS "Average" scores on GB and PM, the F1 CPU is faster by:I dug a bit deeper. In addition to the normal provisioning done in November 2025 I found a suspicious boot from December 2025 during which a USB drive was plugged in. The windows event logs were wiped during that boot, probably to hide the virus install.
I always intended to wipe the drive and install Proxmox on this so I don't care that it came infected. Just warning others that the concerns about malware on these cheap aliexpress mini pcs are legit. Always wipe and reinstall.
Sign up for a Slickdeals account to remove this ad.
DO NOT USE images provided, other than to grab the Windows Product Key from it (ProduKey, JellyBean, ...). Wipe the drive and install from a clean download from Microsoft, or simply install Linux instead.
This is not the case of "single rogue" misdetection. These seem to be purposely placed across various key areas that span all usage possibilities.
Note: I also added a drive letter to the boot partition and the recovery partition and there were no infected files found in either of those. It was only in the core Win11 install.
47 total - Windows 10 Defender 11-APR-2026 from clean installation on it on a separate drive and placing the original drive in external USB reader without ever booting it)
46 total - Subsequent scan with Malwarebytes (after Defender had already deleted 2 most severe automatically without prompting), so this found one fewer net.
Windows defender:
-----------------
PS C:\users\FirebatAM02>
>> Get-MpThreatDetection | Select-Object -Property ThreatID, Resources | Format-List
Virus:Win64/Expiro.DA!MTB
- D:\AMD\WU-CCC2\ccc2_install\Support64\AMDWUTD.exe
- D:\Windows\WinSxS\amd64_microsoft-windows-p..nsimulation-service_31bf3856ad364e35_10.0.26100.5074_none_74b2e4a887a81df4\PerceptionSimulationService.exe
- D:\Program Files\AMD\CNext\CNext\AMDIdentifyWindow.exe
- D:\Program Files\AMD\CNext\CNext\MMLoadDrv.exe
- D:\Program Files\AMD\CNext\CNext\videotrim.exe
- D:\Program Files\AMD\CNext\CNext\7z.exe
- D:\Windows\WinSxS\amd64_openssh-common-components-onecore_31bf3856ad364e35_10.0.26100.5074_none_589a4a3b5f9fb2dc\ssh-agent.exe
- D:\Program Files\AMD\AMDInstallManager\7z.exe
- D:\AMD\WU-CCC2\ccc2_install\Support64\CCC2App64.exe
- D:\Program Files\AMD\CNext\CNext\MMLoadDrvPXDiscrete.exe
- D:\Program Files\AMD\CNext\CNext\cncmd.exe
- D:\Program Files\AMD\CNext\CNext\DuplicateDesktop.exe
- D:\Program Files\AMD\CNext\CNext\amdow.exe
- D:\Program Files (x86)\REALTEK\Realtek Bluetooth\devcon.exe
- D:\Program Files\AMD\CNext\CNext\RSServCmd.exe
- D:\Program Files\AMD\CNext\CNext\CompressionUtility.exe
- D:\Windows\System32\OpenSSH\ssh-agent.exe
- D:\Program Files\AMD\CNext\CNext\PresentMon-x64.exe
- D:\Program Files\AMD\CNext\CNext\LauncherRSXRuntime.exe
- D:\Windows\System32\PerceptionSimulation\PerceptionSimulationService.exe
Virus:Win32/Expiro.HNW!MTB- D:\Program Files\AMD\CNext\CNext\AMDRSServ.exe
- D:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.106\elevation_service.exe
- D:\Program Files\AMD\AMDInstallManager\AMDInstallManager.exe
- D:\Windows\System32\ReFsDedupSvc.exe
- D:\Windows\WinSxS\amd64_microsoft-windows-sensordataservice_31bf3856ad364e35_10.0.26100.4768_none_99aaa7c1da5624aa\SensorDataService.exe
- D:\Program Files (x86)\Microsoft\EdgeWebView\Application\122.0.2365.106\elevation_service.exe
- D:\Program Files\AMD\CNext\CNext\AMDImageLocalizer.exe
- D:\Program Files\AMD\CNext\CNext\QtWebEngineProcess.exe
- D:\Program Files\AMD\CNext\CNext\AMDAIInferencing.exe
- D:\AMD\WU-CCC2\ccc2_install\WULaunchApp.exe
- D:\Windows\WinSxS\amd64_microsoft-windows-storage-refsdedupsvc_31bf3856ad364e35_10.0.26100.5074_none73cfaa1ab0c2b2d4\ReFsDedupSvc.exe
- D:\Program Files\AMD\CNext\CNext\AMDRSSrcExt.exe
- D:\Windows\System32\SensorDataService.exe
- D:\Program Files\Windows Media Player\wmpnetwk.exe
- D:\Program Files (x86)\Microsoft\EdgeCore\122.0.2365.106\elevation_service.exe
- D:\Program Files\AMD\CNext\CNext\amddmlfilters.exe
- D:\Program Files (x86)\REALTEK\Realtek Bluetooth\RtkBtManServ.exe
- D:\Windows\WinSxS\amd64_microsoft-windows-wmpnss-service_31bf3856ad364e35_10.0.26100.5074_none_9f7a99417e73fbce\wmpnetwk.exe
- D:\Program Files\AMD\CNext\CNext\AMDOCApp.exe
Virus:Win32/Expiro.AA!MTB- D:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe
- D:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.27\MicrosoftEdgeUpdate.exe
- D:\Recovery\OEM\Backup\CDate.exe
- D:\Program Files (x86)\REALTEK\PCI-E Wireless LAN WiFi 6 Driver\FindRtl.exe
Trojan:Win32/Phonzy.B!ml- D:\Windows\SysWOW64\perfhost.exe
- D:\Windows\WinSxS\wow64_microsoft-windows-p..structure-minkernel_31bf3856ad364e35_10.0.26100.4202_none_7f2103169b2118aa\perfhost.exe
Worm:Win32/AutoRun!pz- D:\ProgramData\Synaptics\Synaptics.exe
Virus:Win64/Expiro.HNW!MTB- D:\Program Files (x86)\REALTEK\PCI-E Wireless LAN WiFi 6 Driver\SetDrvAll.exe
Virus:Win32/Expiro.EK!MTB- D:\Program Files\AMD\CNext\CNext\RadeonSoftware.exe
Malware bytes:--------------
Registry Key: 2
Virus.M0yv Signature: 6083, 1172559, EB4659F88D6C38468EA2894A
- HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\IMAGE FILE EXECUTION OPTIONS\MICROSOFTEDGEUPDATE.EXE
- HKLM\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS NT\CURRENTVERSION\IMAGE FILE EXECUTION OPTIONS\MICROSOFTEDGEUPDATE.EXE
File: 44Virus.M0yv Signature: 6083, 1168760, EB4659F88D6C38468EA2894A
- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\AMDOW.EXE
- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\VIDEOTRIM.EXE
- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\COMPRESSIONUTILITY.EXE
- D:\PROGRAM FILES\AMD\AMDINSTALLMANAGER\7Z.EXE
- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\7Z.EXE
- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\AMDIDENTIFYWINDOW.EXE
- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\DUPLICATEDESKTOP.EXE
- D:\PROGRAM FILES (X86)\REALTEK\REALTEK BLUETOOTH\DEVCON.EXE
Virus.M0yv Signature: 6083, 1169691, EB4659F88D6C38468EA2894A- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\AMDDMLFILTERS.EXE
- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\AMDRSSRCEXT.EXE
- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\AMDIMAGELOCALIZER.EXE
- D:\PROGRAM FILES (X86)\REALTEK\REALTEK BLUETOOTH\RTKBTMANSERV.EXE
Virus.M0yv Signature: 6083, 1169961, EB4659F88D6C38468EA2894A- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\AMDAIINFERENCING.EXE
Virus.M0yv Signature: 6083, 1169961, 0000000000000000000007D9- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\AMDRSSERV.EXE
Virus.M0yv Signature: 6083, 1174317, EB4659F88D6C38468EA2894A- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\AMDOCAPP.EXE
- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\QTWEBENGINEPROCESS.EXE
VirTool.M0yv Signature: 6602, 1206717, EB4659F88D6C38468EA2894A- D:\AMD\WU-CCC2\CCC2_INSTALL\SUPPORT64\CCC2APP64.EXE
- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\RSSERVCMD.EXE
- D:\AMD\WU-CCC2\CCC2_INSTALL\SUPPORT64\AMDWUTD.EXE
- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\PRESENTMON-X64.EXE
- D:\WINDOWS\SYSTEM32\PERCEPTIONSIMULATION\PERCEPTIONSIMULATIONSERVICE.EXE
- D:\WINDOWS\SYSTEM32\OPENSSH\SSH-AGENT.EXE
- D:\WINDOWS\WINSXS\AMD64_MICROSOFT-WINDOWS-P..NSIMULATION-SERVICE_31BF3856AD364E35_10.0.26100.5074_NONE_74B2E4A887A81DF4\PERCEPTIONSIMULATIONSERVICE.EXE
- D:\WINDOWS\WINSXS\AMD64_OPENSSH-COMMON-COMPONENTS-ONECORE_31BF3856AD364E35_10.0.26100.5074_NONE_589A4A3B5F9FB2DC\SSH-AGENT.EXE
Virus.M0yv Signature: 6083, 1169692, EB4659F88D6C38468EA2894A- D:\AMD\WU-CCC2\CCC2_INSTALL\WULAUNCHAPP.EXE
Virus.M0yv Signature: 6083, 1361069, 0000000000000000000007D9- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\LAUNCHERRSXRUNTIME.EXE
Virus.M0yv Signature: 6083, 1168760, 0000000000000000000007D9- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\MMLOADDRV.EXE
- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\CNCMD.EXE
- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\MMLOADDRVPXDISCRETE.EXE
Virus.M0yv Signature: 6083, 1186904, EB4659F88D6C38468EA2894A- D:\PROGRAM FILES\AMD\CNEXT\CNEXT\RADEONSOFTWARE.EXE
Virus.M0yv Signature: 6083, 1172559, EB4659F88D6C38468EA2894A- D:\PROGRAM FILES (X86)\MICROSOFT\EDGEUPDATE\1.3.185.27\MICROSOFTEDGEUPDATE.EXE
- D:\PROGRAM FILES (X86)\MICROSOFT\EDGEUPDATE\MICROSOFTEDGEUPDATE.EXE
Virus.M0yv Signature: 6083, 1181339, EB4659F88D6C38468EA2894A- D:\PROGRAM FILES (X86)\MICROSOFT\EDGE\APPLICATION\122.0.2365.106\ELEVATION_SERVICE.EXE
- D:\PROGRAM FILES (X86)\MICROSOFT\EDGECORE\122.0.2365.106\ELEVATION_SERVICE.EXE
- D:\PROGRAM FILES (X86)\MICROSOFT\EDGEWEBVIEW\APPLICATION\122.0.2365.106\ELEVATION_SERVICE.EXE
Neshta.Virus.FileInfector.DDS Signature: 1000002, 0, EB4659F88D6C38468EA2894A- D:\PROGRAM FILES (X86)\REALTEK\PCI-E WIRELESS LAN WIFI 6 DRIVER\SETDRVALL.EXE
- D:\PROGRAM FILES (X86)\REALTEK\PCI-E WIRELESS LAN WIFI 6 DRIVER\FINDRTL.EXE
Malware.AI.2393016650 Signature: 1000000, 0, EB4659F88D6C38468EA2894A- D:\RECOVERY\OEM\BACKUP\CDATE.EXE
Virus.M0yv Signature: 6083, 1169715, EB4659F88D6C38468EA2894A- D:\WINDOWS\SYSTEM32\SENSORDATASERVICE.EXE
- D:\WINDOWS\SYSTEM32\REFSDEDUPSVC.EXE
- D:\WINDOWS\WINSXS\AMD64_MICROSOFT-WINDOWS-STORAGE-REFSDEDUPSVC_31BF3856AD364E35_10.0.26100.5074_NONE_73CFAA1AB0C2B2D4\REFSDEDUPSVC.EXE
- D:\WINDOWS\WINSXS\AMD64_MICROSOFT-WINDOWS-SENSORDATASERVICE_31BF3856AD364E35_10.0.26100.4768_NONE_99AAA7C1DA5624AA\SENSORDATASERVICE.EXE
Virus.M0yv Signature: 6083, 1191010, EB4659F88D6C38468EA2894ADisconnecting the Firebat AM02 from ethernet and re-installing the original Win11 NVMe drive and completing setup, I can confirm that it actively infects EVERY .EXE file opened whether on the primary drive or launched from a USB stick. Every-single-one. Luckily it doesn't try to deeply hide the activity as I can immediately get warnings from Windows Defender that it detected a virus in a previously safe file. Every one I copied from a backup drive to a temporary USB stick that was safe going in, got corrupted after launching in the Win11 install on the Firebat. Taking the USB stick to a different computer verified the same thing (it wasn't a corrupted scanner instance on the Firebat).
Worst part of all of this: I had quarantined / deleted every file from the bad Win11 NVMe when I still had it on USB adaptor scanning it from a safe Win10 install on a different booted NVMe. This means that stuff was hidden enough from scanners on that unbooted image, so then on completing the installation once connecting Win11, the viruses came back to life somewhere.
And, after the first day thinking that Win10 installed, activated correctly, I did get a warning it had been installed on another PC today. Only when I finally booted the virus filled Win11 image did it then show it as active. After trying to install a safe new download of Win11 to a clean new drive it failed to activate. It did show the last 5 character which were the same (so it must be stored in BIOS), but now with the different drive installed it is refusing to register as the same hardware. Of course I am under no assumptions these are in anyway legit keys of course and fully expect it to be disabled at some point in the future. I didn't buy it thinking it actually was a valid key, or virus-free installation.
I have not tried to replace the files on the original drive with clean ones yet to see if it will sense that it is the same hardware and say it is a valid license.
Again: DO NOT USE THE WIN11 IMAGE THAT COMES PREINSTALLED!!!! (And likely the ones they have on their download page linked to Google drive!) Download fresh from Microsoft and wipe the entire NVMe they ship. I will update if I get it to reinstall fresh using the stored key, back onto the original drive that came with it wiping the virus ridden files entirely.
EDIT: I successfully got a clean Win11 image installed replacing the bad one on the original NVMe drive. The product key assigned, even though stored in BIOS, it a hardware matched key not a general supplier matched key (e.g. Dell). That means you cannot change the NVMe drive for a different one as Microsoft product activation sees that as a new system and invalidates the activation.
Here is what you do (simple steps for experts, no backup taken, bare metal) to replace the virus ridden image.
1) QUICK format the primary install (400+ GB) partition. DO NOT delete/recreate, the GPT GUID's are possibly part of what the license is tied to
2) Boot from USB using latest download from Microsoft to install. Chose "fresh, accept deleting all files" and select just the reformatted one.
That's it! On re-entry, since you are using the same drive with the same partition, it will show your license is active.
Longer steps for those less techie:
1) Download the Media Creation Tool for Win11 from Microsoft and create a USB stick with the latest Win11 Home 25H2 image.
1a) I HIGHLY recommend downloading the ISO first instead of having the MCT directly write the drive. Then you can install Rufus to not only write the drive but also check its box to create the file that bypasses the requirement for Microsoft account, allowing you to use a local account only instead
2) (Backup safety) Using a program such as Disk Genius that properly understand and reports all GUID information associated with the drive and volume, and has built in backup, take a full "Disk" backup of the NVMe when installed in a separate machine through external USB<>NVMe adaptor. DO NOT BOOT that drive with the virus laden Win11 image. By taking this backup if you ever trash that included drive you can get exactly back to the original layout to start over, not losing your product key activation.
2b) HINT: Before taking the backup delete the HIBERFIL.SYS and SWAPFILE.SYS to save massive amounts of space on the backup. The backup of the whole disk should be around 10GB using the maximum compression level in DiskGenius
2c) Also consider running a Powershell script (or take screenshots from DiskGenius) showing each GPT GUID for each volume and the drive as a whole just in case.
3) After creating the backup, when still connected on the other drive, use standard Windows Explorer or Disk Management and find the large 400+GB volume labeled Windows on the NVMe drive, and chose "Quick Format" and default of NTFS.
4) Move the drive back into the Firebat, and then place the USB stick in the front port to install Win11 clean
5) Turn on the firebat and keep repeatedly pressing F7 until you get a DOS-like screen letting you select which device to boot from, chose the USB port not the Firebat NVMe drive
6) Follow the normal install process for Windows, selecting the large 400GB+ empty volume (DO NOT reformat it or delete or anything else--all other partitions including recovery did not show any sign of viruses when I scanned)
7) If you burned with Rufus and chose the local account only option, you should be good. If you forgot to do that and don't want the forced Microsoft account, do these steps when it asks for your online account during setup:
7a) SHIFT-F10 (opens a command prompt)
7b) Type: "start ms-cxh:localonly" and then a separate window will open letting you create a local account with password and 3 security questions. Finishing this will take you back to the rest of the install automatically
That's it, finish the install process and you now have a completely safe clean Win11 install. Since that install is tied to the original drive, I would strongly suggest if you want to install other operating systems such as Linux, take that drive out and use an alternate NVMe drive.
And as noted a few posts back, I verified that the M.2 slots ONLY support NVMe protocol and therefore you cannot place SATA only drives, whether a M.2 NGFF connection (B+M key) or any B+M key adaptors to convert to a normal SATA 2.5" connector. These devices are stuck with NVMe only (not a bad thing but can't use the 2.5" mounting slot in the bottom case for older drives as secondary, internally). These will have to connect externally through USB adaptors instead.
Mine is also full of expiro viruses. A full wipe and usb install of windows took care of that.
Mine also had a loose screw from the second M.2 drive floating around.
Leave a Comment